Innovation and Effectiveness in Cyber Security
Automated UDP Scanning via Zmap
One of the essential steps for hackers or penetration testers before taking over a system or an infrastructure is to get full knowledge about it. This is what so called a reconnaissance phase which can be performed either passively or actively to collect information about the target through various information gathering mechanisms. Port scanning using tools like zmap is an effective active reconnaissance method due to its speed and simplicity to clearly map the intended target. In this writing, we will demonstrate some of the zmap tool capabilities that helps gathering interesting information.
Putting the tool in action will basically reveal all open ports of a target system and hence it determines the potential services running behind each identified open port. This information is necessary to start discovering all vulnerabilities that would allow for an initial access. However, port scanning is very noisy and can be easily detected especially when a penetration tester does not know the security perimeter and all other in-place security measures. If scanning tool is not used correctly, especially from script kiddies who usually run it in an aggressive mode, the penetration testing attempt is discovered and scrutinized by defender team.
Port scanning: To get hands around scanning, let us explore more about the port scanner tool functionalities and how the relevant protocols react. The main two important protocols from TCP/IP family in subject are the transport protocols TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). Each of them has a 16 bits long port number field which enables a range of ports from 0 to 65535 that can be classified as reserved for a special purpose, dedicated to a certain application, or unknown. A port scanner determines a port status by sending a request, optionally with adjusted parameters, and wait for a response. The TCP protocol, as it is a connection-oriented protocol, will respond back with clear message. In contrast, UDP, which is a connection less protocol, might not react to queries as expected. Some well-known standard services as of DNS, SNMP, and DHCP run over UDP are excellent examples for such scan challenges. That is, unlike TCP it is hard to detect UDP ports as they might not respond back to requests sent. To make this happen, we adjust a specific payload in the transmitted packet to force a UDP server service to react. Zmap port scanner enables us to perform such operation also automatically and that is a good reason for choosing it over others.
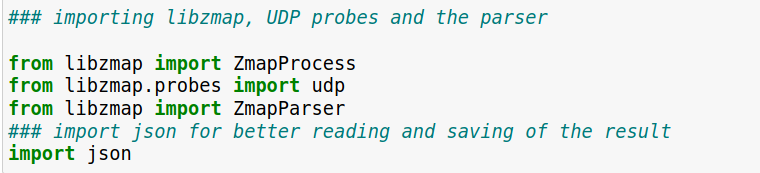
Code snippet: We used Python (3.8) and the libzmap-python3 library. The latter allows to scan UDP and TCP ports using zmap, and it contains a parser to parse the results in a json format in order to save them. Zmap is a port scanner used for large-scale scanning and is considered one of the fastest scanning tools. Zmap uses many UDP probes (payload packets), which can help identifying open UDP ports. The importing of libzmap library in our code is illustrated below.
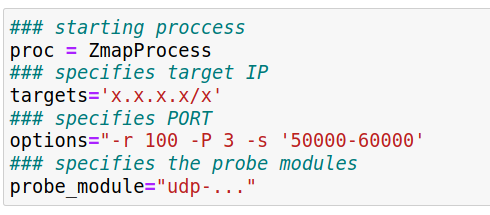
After sending the request, zmap waits for the response and pass the raw data to the parser, which parses and sends the data to an elasticsearch or any other database for further processing. The calling of the Zmap process in our code is illustrated below:
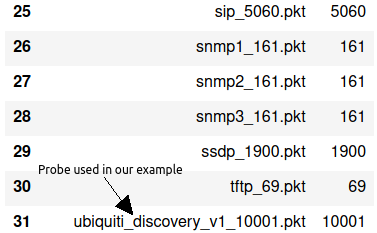
Probes are selected by the user in a config file depending on what UDP services need to be scanned, as mentioned before:
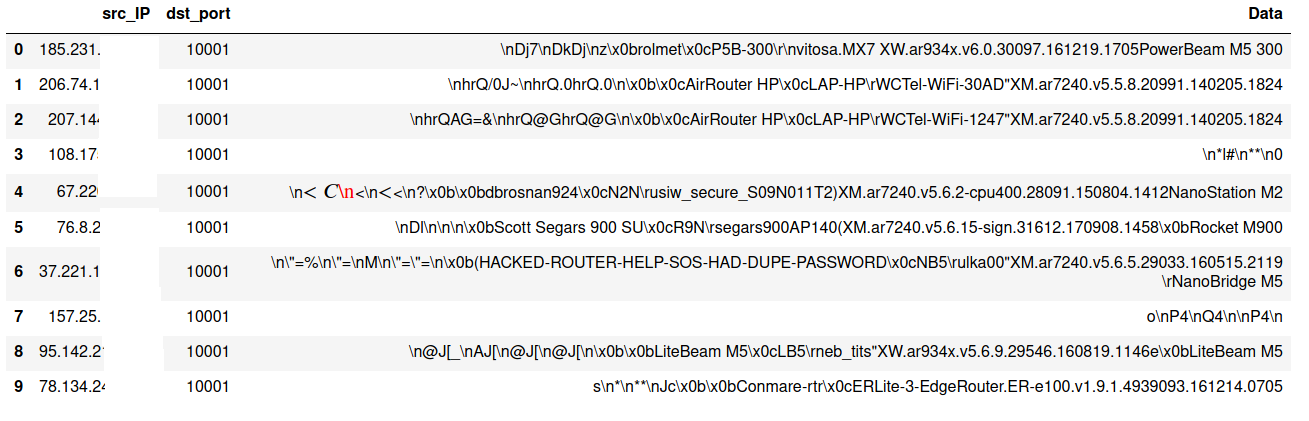
A snippet of example raw results, which are generated by zmap and sent to the parser, is illustrated below.