
Innovation and Effectiveness in Cyber Security
Summary of Findings
The Lebanon Cybersecurity Empowering Research Team presents hereby a third attack surface evaluation of the Lebanese perimeter. Selected 20 critical software vulnerabilities, 612 608 IP Addresses, 67 699 live hosts and 86 525 domains were analyzed. The selected vulnerabilities were chosen based on their high or critical rating according to the CVSS scoring system, and because they have been being actively exploited according to threat reports. The study focused on the second quarter Q2 of 2021 to mainly identify the corresponding vulnerable systems during that period. It was found that 976 systems are vulnerable affecting the majority of Lebanon's sectors, including critical infrastructure.
Key Trends in Q2 2021
Before deep diving in the results of our attack surface evaluation, this section presents a recap of security highlights from Q2 2021, which are related to the vulnerabilties addressed in this study.
- More hacking groups attack Microsoft Exchange: Unpatched Exchange servers were hunted down by several state-sponsored hacking groups and the attacks targeted tens of thousands of on-premise impacted systems. The telemetry of threat actors went beyond the big known APTs as “Hafinum” or “Calypso” to show also additional yet-unclassified clusters taking the advantage of the four Exchange flaws deploying web shells on thousands of unique Exchange servers from over 115 countries.
- APT hacked a US municipal government via unpatched Fortinet VPN: Foreign hackers compromised the network of a local US municipal government by exploiting flaws in an unpatched Fortinet VPN as reported by the Federal Bureau of Investigation (FBI). Threat actors gained persistence on the network after having created an account that looked like other standard accounts.
- Chinese cyber espionage target Pulse Secure VPN: Cybersecurity researchers from FireEye unmasked TTPs adopted by Chinese threat actors of getting an initial foothold on attached networks using Pulse Secure vulnerability. This allowed adversaries to steal credentials, escalate privileges, and conduct internal reconnaissance after a successful initial access.
- QNAP NAS flaws exploited in ransomware attacks: QNAP network attached storage (NAS) devices were targeted by “Qlocker” ransomware and adversaries demanded 0.01 bitcoin for the decryption key. Another ransomware family named eCH0raix was also deployed by threat actors to lock sensitive data by leveraging known vulnerabilities. QNAp urges users for malware removal, perform a scan, apply latest patches, and modify default network ports accessing the operating interface.
- United Nations breach exposed 100K+ staff records (compliance violation): Poorly secured git servers containing configuration files that include credentials for other servers allowed researchers to exploit a vulnerability and log in to a database server and access employee’s private data.
Critical Vulnerability Analysis
One main goal of this study is to evaluate the number of open critical vulnerabilities in the Lebanese perimeter during the second quarter Q2 in 2021. The latter is depicted in the figure below. Here the total number of vulnerabilities in Q2 is plotted as well as a split of those that were found new in Q2 2021, and those that were also open in Q1 2021.
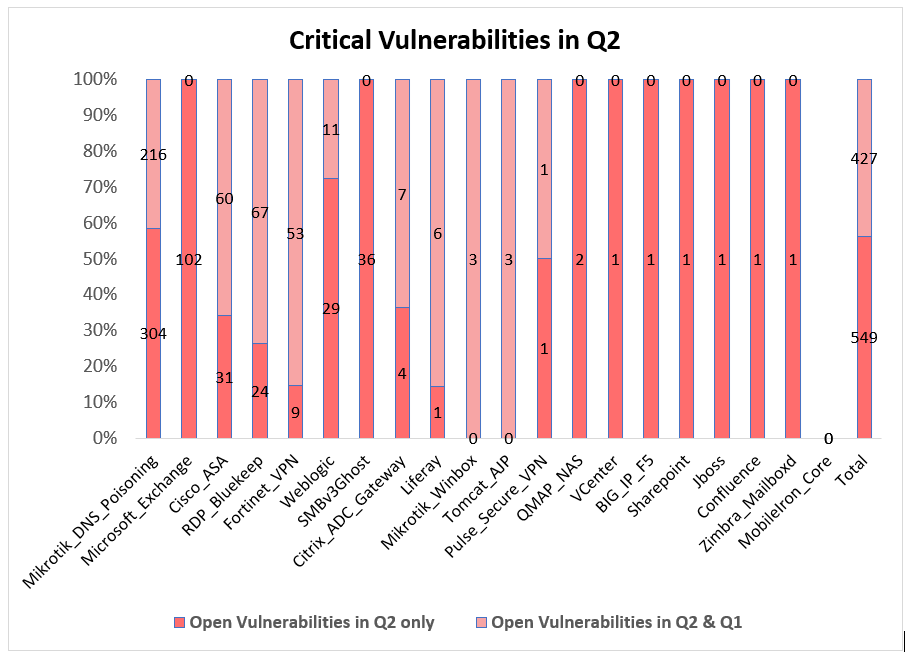
Based on this figure, we would like to mainly shed the light on two observations. 1) Especially noteworthy are the 102 Microsoft Exchange servers, which are exposed to critical vulnerabilities published the end of march 2021. This shows that Lebanon could strongly be affected by vulnerability research activities in the world. This underlines the need for a trusted (national) entity that provides relevant threat reports to the Lebanese sectors in time. 2) A non-negligible number of relatively old vulnerabilities like Cisco ASA firewall, intensively exploited by threat actors, are found to be open in both Q2 and Q1. Given that this firewall is mainly used for non-private purposes in Lebanon, this result in addition to the more than 100 systems exposed to Fortinet VPN, Citrix, and other vulnerabilities indicate the lack of patch management awareness. Here, our notification attempts [2,3] do not seem to be yielding significant improvements. In contrary, despite the fact that the attacks on the vulnerabilities identified and reported by our team can be very impactful for many victims, the number of some of the reported vulnerabilities is increasing instead of decreasing (see mikrotik DNS poisoning). This again stresses the importance of a trusted (national) reference for notification purposes as well.
Impacted Sectors by Critical Vulnerabilities
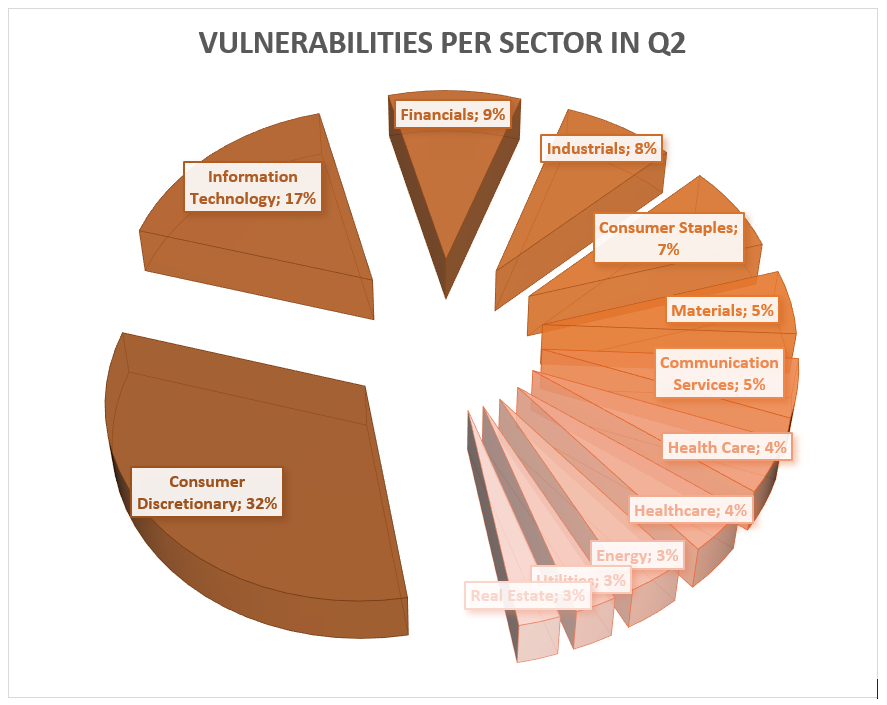
Focusing now on the most affected sectors, among the 205 sectorized vulnerable systems, the figure below shows that the Consumer Discretionary and the Information Technology sectors are the most affected ones with a total of 32% and 16.5% vulnerable systems, respectively. The Financials and Industrials sector come next with 8% and 7%, respectively. Other sectors like Healthcare, Communication, Energy, Real Estate, and Utilities occupy between 3% and 5%.
In other words, this study Unfortunately shows that the vulnerabilities are affecting the majority of the lebanese sectors, including critical infrastructure! In fact, further results reveal that some critical infrastructure sectors like Financials and Industrials have not even closed aged vulnerabilities as of Citrix Application applications exploited by Speculoos, and Windows Server Message Block exploited by various threat actors.
Compliance Violation Analysis
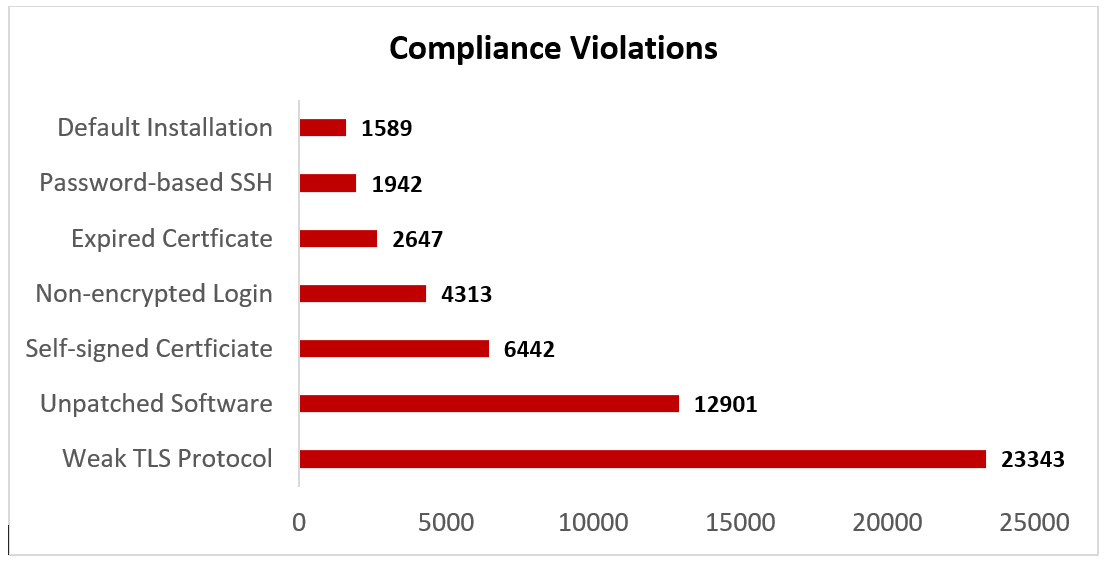
The examination of over 67K systems for violations of security best practices as per the Center of Internet Security (CIS) framework shows that the highest discovery of compliance violations is in the protocol used to facilitate privacy and secure communication over the Internet. As the figure below shows, a huge number of systems use a weak TLS protocol in addition to the use of non-trusted self-signed certificates or expired certificates. Also noteworthy are the 12901 unpatched systems/services/libraries/frameworks, which confirm the high number of critical vulnerabilities found in our studies [1,2,3,4]. Yet, especially noteworthy is the relatively high number of unencrypted login services . That is, sending usernames and passwords in cleartext over the Internet through all corresponding network elements (routers, proxies, etc.) worldwide. This means admins of those networks elements and entities with access to those network elements have also access to the credentials of the lebanese users, which are using the non-encrypted login service. The remaining compliance violations speak for themselves!
Ethical Considerations
We take various steps to follow research best practices during our studies. Among others, we stick to the following.
- Scan: Lebanon Cybersecurity Empowering Research Team performs only unauthenticated scans to systems exposed to the Internet. The scan itself is not intrusive and doesn’t introduce any denial of service, denial of access, or a risk of interruption of business.
- Data Collection: Information systems are queried on a quarter basis, typically looking for open ports and Internet facing system information on the discovered ports.
- Information Sharing: Risky collected information is made available only to the system owners and not shared with any third party but law enforcement.
References
[1] Aljadeed TV, Jan. 2021, https://www.aljadeed.tv/arabic/news/lebanoncert/critical-vulns[2] Lebanon CERT, Jan. 2021, https://lebanoncert.org/study-q4-2020
[3] Ali Awad, Al Akhbar, Sep. 2020, https://al-akhbar.com/lebanoncert/critical-vulns
[4] Lebanon CERT, Jun. 2020, https://lebanoncert.org/study-q1-2020
