
Innovation and Effectiveness in Cyber Security
Automated Reporting of Vulnerabilities to Impacted System Owners
Gathering e-mail addresses pertaining to impacted domains with critical vulnerabilities is an essential milestone in the vulnerability management and discovery process. One of the biggest challenges is to ensure email records are accurately fetched so reported vulnerabilities are properly addressed allowing system owners to take an immediate action. Lebanon CERT team proved again as part of their research capabilities to take OSINT advantage and build a tool, Contact Hound, that automatically collects the required information from the internet and apply the right sorting, purging, and filtering mechanisms.
Gathering emails: An essential functionality of the Contact Hound tool is to search & find each and every e-mail address of the scanned domains. This is approached through the following methods:
- Using the "Advanced Search" feature implemented to most search engines.
- Scraping homepage and Contact page of the investigated domain.
- Query WHOIS, the widely known internet service, to get owners and contact information of a domain
A quick research concluded that various search engines, some listed below, are capable of delivering the expected results:
- Ask
- Bing
- Yahoo
- Baidu
- Yandex
- Exalead
- Dogpile
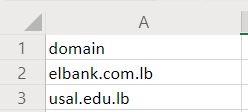
Test run: The following example demonstrates the email gathering using Contact Hound tool.
At first, we create a csv file with all required values as depicted in the figure below:
We then launch Contact Hound command line tool to start the gathering process. The following command syntax takes previously created file as an input, appended by a tag specifying the searched value (domains in our case) and saves the results to an output file.
python CHound.py --emailgather -f demo.csv -t 1 -o results.csv
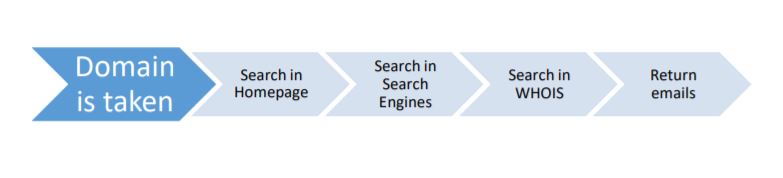
Processes performed by the script are illustrated in below diagram:
A code snippet of searching in search engines like Yandex using the Contact Hound tool is illustrated below.
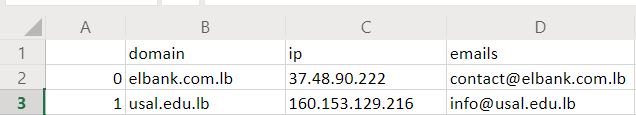
 Final Results: It is very important to have an accurate results. For the sake of demonstration we have used a simple syntax to obtain our results, however the tool can be programmed in a way to deliver different result sets.
Final Results: It is very important to have an accurate results. For the sake of demonstration we have used a simple syntax to obtain our results, however the tool can be programmed in a way to deliver different result sets.
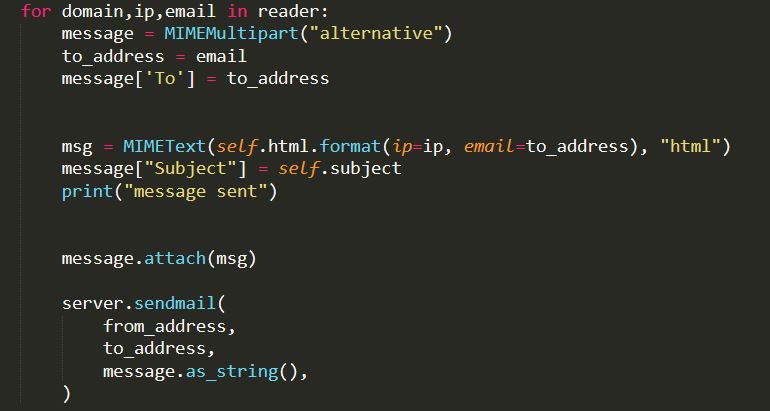
Sending emails: Having all necessary data collected, we are now ready to inform respective system owners. The process is straightforward:
- Dump all the data, as of recipient email, affected domain, system IPv4 address, and other custom variables, to csv or json file.
- Configure Google SMTP server using smtplib and ssl python modules to send out MIME Multipart messages to the recipients extracted in the previous step.
Conclusion: Using the Contact Hound tool to support multiple Lebanon CERT large scale vulnerability scanning campaigns showed great results. It returned accurate emails with low error rate. Additionally, It almost had absolute return rate due to the inclusion of the WHOIS feature so, for every domain it returned at least one email to contact. We tool and the process will be continuously maintained and upgraded to find better, accurate, and faster results.
